How to prevent your Bitcoin account from getting hacked
One of Bitcoin’s key features is that transactions are irreversible. Once you receive Bitcoin, the sender can’t take back the money.
But it also means that if your account gets hacked, you will have difficulty recovering any stolen cryptocurrency.
You should only deal with reputable Bitcoin companies and learn how to identify scams. But that’s only half the equation.
There are steps you can take to keep your Bitcoin safe:
- Secure your email account
- Secure your social media accounts
- Using unique, strong passwords for all online accounts
- Enable two-factor authentication
- Be vigilant about phishing attempts
Let’s go over them one by one.
Step 1: Secure your email account

The problem
If someone breaks into an unlocked house, takes the car keys from the kitchen counter and drives off with the stolen vehicle, you can’t blame the car company for having a weak security system! The car owner has a weak security system.
When someone says their account was hacked, it usually means their email security was inadequate. Hackers who gain access to your email can control any linked accounts.
They can visit sites you have an account with and request a password reset. When a password gets reset, a link gets sent back to the inbox. After this, hackers may change the email address in your accounts, completely locking you out.
And it snowballs. The more accounts a hacker controls, the easier it gets to compromise others. Some accounts may show your recovery questions, like “Where were you born?” and “What is your mother’s maiden name.” With enough access, they can find this information.
How to secure your email account
1. Use a unique, strong password
A strong and unique password is crucial. If your password is weak, a person or computer program can easily guess it. A good password:
- Includes both upper and lowercase
- Includes a mix of letters, numbers, and punctuation
- Has least six characters — ideally more
- And is only used for that site.
If you don’t have a unique, strong password for your email account, change it now. Failing to do this puts your Bitcoin at risk — and your online banking, social networks, documents and everything else.
Not sure if your password is strong enough? This site tells you how long it would take a computer to hack into your account. For example, the password ‘1234’ would be guessed instantly, whereas ‘2wE30/hh7.’ would take a whole decade to crack.
2. Check your recent login activity
Most reputable email providers allow you to see devices and locations around the world which have accessed your email account.
If you don’t recognise a login session by time, device or country, immediately change your password.
![]()
Useful links:
How to see last account activity on Gmail
Recent account activity on Yahoo!
Recent activity on your Microsoft account
If you use a different email service, reach out to them to ask how to see recent activity.
3. Review and remove email auto forwarders
Most email accounts have a handy feature where you can automatically forward certain email types to another address. If you, for instance, receive a monthly emailed invoice from the telephone company, your email provider can automatically forward a copy of that email to your spouse or your housemate.
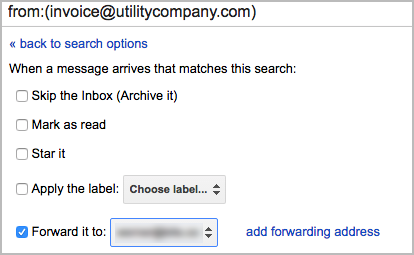
The problem is, if a hacker got access to your email account at any time in the past, they might have set up an auto-forwarder like the one above for specific sensitive emails (or worse yet: for all emails) to be forwarded on to them. These emails can be stored over time and used against you.
HOW TO REMOVE AUTO FORWARDERS:
You can review Gmail settings by clicking Settings (the gear icon) > Forwarding and POP/IMAP.
More links:
- How to add/remove forwarders in Gmail
- How to enable/disable automatic forwarding in Yahoo!
- How to start/stop email forwarding from your Microsoft account
If your provider isn’t listed, check the Settings section to see if there’s anything suspicious or contact them for help.
4. Review linked accounts
Email accounts have another useful feature that can be both good and bad: linked accounts.
Sometimes we’d like to move on from silly old email addresses, like [email protected], to something a little more professional like [email protected]. The problem is that we don’t want to login and manage both or miss any emails still sent to the old address.
In those instances, you can link the two accounts. If you have access to both email accounts, you can connect the old to the new one and all emails will still arrive in your inbox.
You can event set it up that you can send emails from the new account using the other email address.
The problem is, again, if a hacker got access to your account at some stage in the past and linked it to theirs, they can send and receive emails like they are you.
HOW TO REMOVE LINKED ACCOUNTS:
Check for suspicious accounts in Gmail by clicking Settings (the gear icon) > Accounts and Import.
Helpful links:
- Start/Stop email importing in Gmail
- Managing multiple mailboxes in Yahoo! mail
- Managing multiple mailboxes in Microsoft mail
If your email provider isn’t listed, reach out to them directly for more information on linked accounts.
5. Set up two-factor authentication
I’ll go into more detail further down below, but two-factor authentication requires two things to gain access to your email account: something you know (your password) and something you have (your mobile phone).
It is nearly impossible for a stranger to gain access to your email account with two-factor authentication enabled.
Step 2: Secure your social media accounts
Many people interact more frequently with social media platforms than they do with their email accounts. Many social media platforms, like Twitter and Facebook, allow you to authenticate and log in to other websites, without the need for a separate username/password.
It is of critical importance that you secure your social media accounts. The first thing is to ensure a unique, strong password for all social media logins. Also, enable two-factor authentication, if it is available (more information on that further below). Lastly, have a look at sites and apps you have authorised and remove suspicious/inactive ones.
Authorising and revoking apps/accounts on Twitter
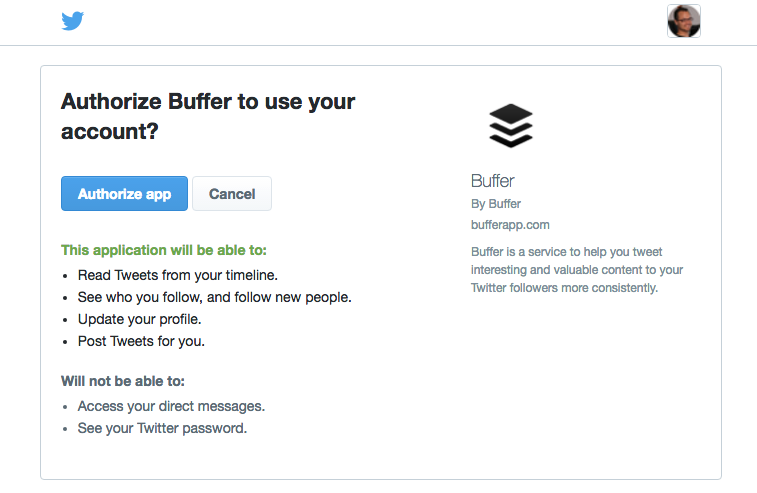
Log in, click on your image and Settings and navigate to Apps.
More: https://support.twitter.com/articles/76052
How to keep your Facebook account secure
Facebook has excellent resources on security:
Go through the entire list, but pay attention to the Passwords, Login Approvals, and Login alerts sections.
Step 3: Use unique, strong passwords
Why should passwords be unique?
As mentioned earlier, if you use the same password on two websites, you are already leaving yourself open to attack.
We sign up for hundreds of online accounts these days. Whereas you might trust Luno to keep your Bitcoin and information secure and not to store your password in an unencrypted form, not all websites have such high security.
It is, as an example, simple for a hacker to set up a website promising you free Bitcoin; where you need to enter an email address and password to get started. If you use the same email and password on all websites, that hacker now has your email address and password to all other accounts. Your other accounts may include sensitive information or cryptocurrencies.
Why should passwords be strong?
It is very simple for a hacker to crack a weak password. If your password contains a mix of numbers and words found in dictionaries, it can be hacked through brute force.
Use a password management tool
It is unreasonable to expect someone to remember hundreds of account passwords, especially strong ones. And writing down your passwords on a piece of paper or online document is not a secure solution.
At the very least, I suggest remembering your unique, secure password for all accounts that contain sensitive information. That said, the easiest, most convenient and secure way is using a password management tool instead.
What is a Password Management Tool?
Password management tools help you to store, organise and use all of your online passwords. They require you to create (and remember) a single, strong password. This gives you access to all your other passwords.
A lot of people ask “So what if the password manager tool gets hacked?”. There is a possibility of it happening, albeit a small one. There’s no such thing as absolute security. However, it’s more likely that you’ll make a mistake trying to protect all your passwords yourself, than it is for a dedicated company
I’d rather trust a dedicated security company that specialises in password management to handle it for me than to rely on saved notes or worse yet: my memory.
Most password management tools also make logging in faster. Once you are logged in on your computer, you can log into websites with a few clicks (without typing out your full email address and password each time). This alone can make your daily workflow more efficient.
Suggested password management tools
We’re in no way affiliated with any of these password managers. It’s up to you to decide which has the right features for your needs. Be sure to always use a strong (and unique) password for your manager.
Tool Details:
LastPass: Highly recommended. Good UX and many features in free and premium versions.
RoboForm: Fast and many features. Lacks password strength reporting & sharing.
DashLane: Powerful, but the free version has very limited features. Can’t save application passwords.
KeyPass : Free, open source alternative.
Step 4: Use two-factor authentication
Two-factor authentication (or 2FA) is one of the best, free ways to secure your online accounts. It is one of the most effective ways to protect yourself and can be done in under two minutes (see our video demo below).
Two-factor authentication adds another layer of authentication to access an account by requiring two things: something you know (your password) and something you have (your mobile device).
Many sites and services already support 2FA, including Google, Facebook and Luno. You might already be used to your bank or credit card provider sending you a text message with a one-time PIN for certain transactions. These services also two-factor authenticated.
How to enable two-factor authentication
You will first need to download a reputable 2FA app onto your mobile device, then you need to set it up on the supported website.
1. DOWNLOAD AND INSTALL A 2FA APP:
The most popular 2FA apps are listed below. Do your research and install one of them on your mobile device.
AppSupported platforms:
Authy: Android, iOS, Chrome, OS XRecommended. Free, multiple devices, good backups & recovery
Google Authenticator: Android, iOS,
BlackBerryOriginal: 2FA app, trusted brand, free
LastPass Authenticator: Android, iOS, Windows phone. Nice LastPass integration, one-tap authentication
FreeOTP: Android, iOSOpen-source alternative by Red Hat
2. SET UP 2FA ON YOUR ONLINE ACCOUNT:
There are many sites that support two-factor authentication. For assistance in setting up, please contact those sites directly.
Below are the setup instructions for Luno:
Navigate to Settings > Security in the menu. Since you’ve already installed a 2FA application, above, click the setup button.
Luno should show you a screen with a QR code which you’ll need to pair your mobile device with Luno.
On your 2FA app:
- Add a new account
- Scan the QR code as shown by Luno
- Save the account
Your 2FA application should show you a six-digit code (that changes every 20–30 seconds)
On Luno:
- Print out the QR code page and store it in a safe place.
- Type in the code generated on your 2FA app
- Click enable
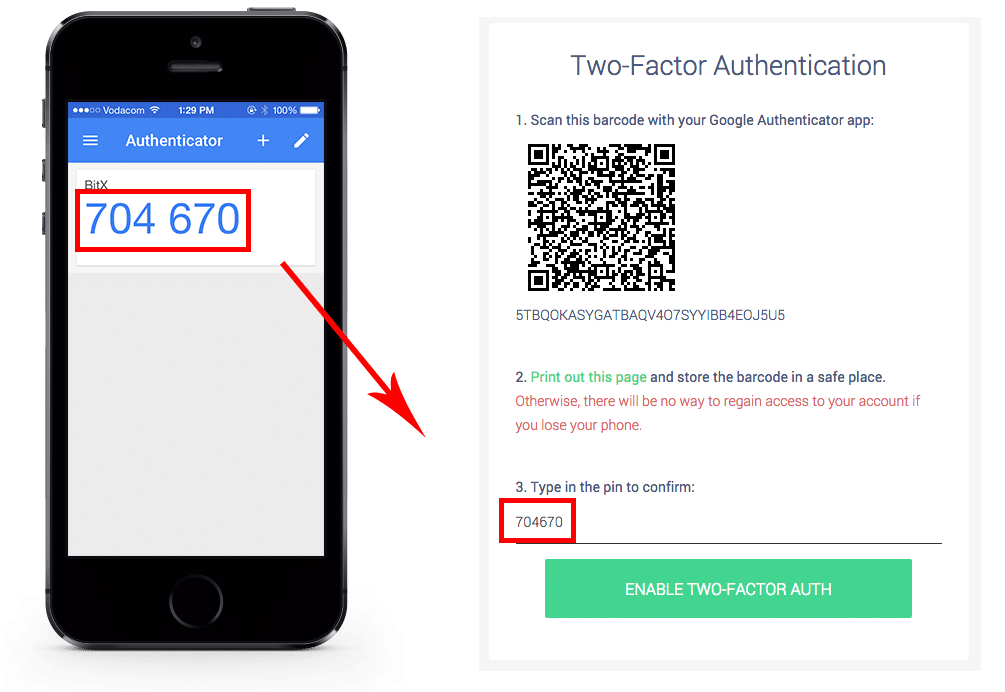
Your phone (2FA app) and Luno are now linked!
Even if someone now managed to steal, guess or otherwise hack their way to get your Luno username and password, they won’t be able to log into your account without the 2FA code.
Step 5: Be vigilant about phishing attempts
Phishing is a form of fraud in which the attacker poses as a reputable company (in this case, Luno) and tries to steal personal details such as your sign-up information or authorisation codes. Phishing can take many forms: SMS, email, and phone call.
It’s important to always remember that Luno will never ask you to confirm your bank details, password, or any other security codes via phone call. And we’ll never threaten to terminate your account via SMS if you don’t perform an action. Learn more about phishing attacks here.
At Luno, we’re dedicated to keeping your personal information and cryptocurrency secure, but keeping your account safe is a joint effort.
Identify Phishing emails
Here are some tips on how to determine whether an email is legitimate or not:
1. Identify the sender
- Always check the “from:” address in emails.
- Ask yourself if you’re expecting an email from the sender?
2. Screen the links
- Hover over any links to see the real website address they go to before you click on them
- Images or buttons can also contain links to potentially malicious websites
3. Don’t trust attachments
- If the email seems suspicious do not open any attachments
- Attachments with malicious software can be disguised as documents, PDF’s or zipped files
4. These are the only official Luno email addresses we use for various types of communication with our customers:
- [email protected]
- [email protected]
- @engage.luno.com
- @announcement.luno.com
In closing
There are certain things that your Bitcoin provider should do to keep your Bitcoin secure. Luno keeps our customers’ Bitcoin safe, but there are certain things that you need to do to protect yourself.
If you think your account has been compromised, immediately reach out to us at [email protected]
 Discover
Discover Help Centre
Help Centre Status
Status Company
Company Careers
Careers Press
Press
